
Quantum-Safe Migration: Understanding the Real Sources of Cost
Introduction
As governments and enterprises begin their quantum-safe journeys, many are still working to understand the full scale of the task ahead. Migration is likely to take years, not months, and the associated costs will vary significantly depending on the size, complexity and condition of the systems being remediated. This uncertainty is reflected in the way the market discusses quantum-safe migration costs: numbers of varying magnitude tend to be thrown around. Some estimates focus narrowly on cryptographic tooling, while others include infrastructure replacement, systems integration, enterprise transformation, programme management and long-running remediation activity. That is why headline figures can be difficult to compare.
The US Federal Government’s PQC migration estimate is a useful illustration of this challenge. In its 2024 report, the Office of the National Cyber Director projected that migrating prioritised federal information systems to PQC would cost approximately $7.1 billion between 2025 and 2035, in 2024 dollars. The important insight is not just the size of the number, but what appears to be driving it. Agencies were required to account for the specific conditions of their host systems and networks. In some cases, they identified systems that could not accommodate new cryptographic implementations, including systems where algorithms were hardwired into hardware or firmware, or where the system lacked the capacity to accept replacement algorithms. The cost of replacing those systems was described as a significant portion of the overall estimate.
This distinction is critical. It shows that the largest costs in quantum-safe migration may not sit in the obvious categories of new tooling or specialist cryptographic products. They sit in the wider estate: legacy platforms, embedded systems, networking equipment, security appliances and enterprise technologies where cryptography is deeply integrated but difficult to modify. This also highlights why cost cannot be separated from risk. The urgency and cost of remediation will depend on factors such as data sensitivity, asset lifetime, system criticality and technical flexibility. Some systems will need to be remediated early, particularly where they protect sensitive, regulated or long-lived data. Others may transition gradually through natural vendor refresh cycles, while some long-lived or operationally sensitive assets may require compensating controls rather than direct replacement.
A further challenge is that responsibility for quantum-safe migration is rarely concentrated within a single team or budget. While discovery, governance and risk assessment are often led by cybersecurity and enterprise architecture functions, the underlying remediation activity frequently sits within infrastructure, networking, cloud, application, telecommunications and operational technology teams. In many organisations, the largest costs are therefore likely to emerge outside traditional cybersecurity budgets, embedded instead within broader infrastructure refresh, operational resilience and digital transformation programmes. Quantum-safe migration is therefore not simply a cryptographic upgrade programme, but a distributed enterprise transformation challenge that requires coordinated governance, funding and prioritisation across the wider technology estate.
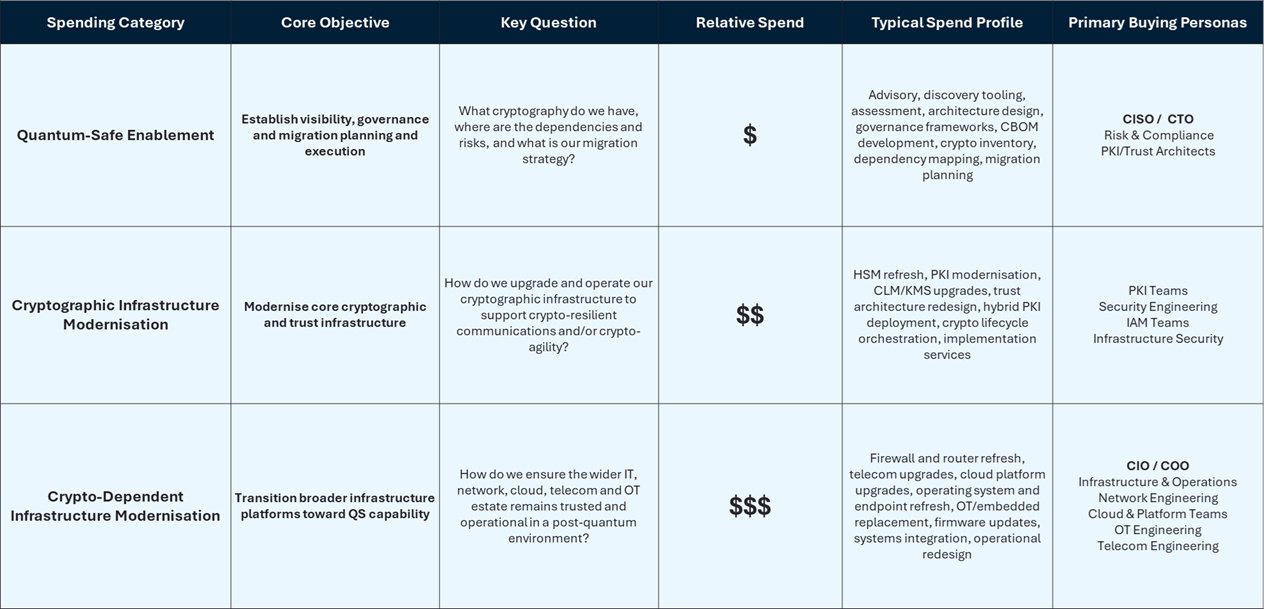
To bring greater structure and clarity to these discussions, we segment quantum-safe expenditure into three broad categories: Quantum-Safe Enablement, Cryptographic Infrastructure Modernisation, and Crypto-Dependent Infrastructure Modernisation. Together, these categories help explain where expenditure is likely to emerge, who is likely to own it, and why migration costs can vary so significantly between organisations.
1. QS Enablement
Quantum-safe enablement refers to the services, governance frameworks and software tooling required to discover cryptographic assets and dependencies, establish a Cryptographic Bill of Materials (CBOM), assess cryptographic risk, and plan the transition toward crypto-agility and quantum-safe architectures. It represents the first stage of most customer programmes, providing organisations with visibility into where cryptography is used, how it is implemented, and which systems, applications, protocols and operational processes may be affected by future cryptographic change.
Initial expenditure is typically weighted toward strategic advisory, assessment, architecture and transformation planning services, alongside new discovery and orchestration tooling designed to address challenges that did not generally exist in classical cryptographic environments. These include cryptographic inventory, dependency mapping, algorithm and protocol discovery, certificate and key visibility, policy management and remediation planning across complex IT, OT, cloud, telecom and embedded environments.
Within the crypto-agility domain, quantum-safe enablement focuses on providing the visibility, governance, architectural understanding and planning frameworks required to support future cryptographic transition. This includes identifying cryptographic dependencies, assessing crypto-agility readiness, defining target architectures, establishing migration priorities, and developing the policies and operational models required to support long-term cryptographic change. As this matures, expenditure within this category will transition from discovery and inventory tools and processes to ‘Post-Quantum Cryptography Implementations.’ This includes abstraction libraries, hybrid application protocols and governance & audit reporting amongst others.
Within the crypto-resilience domain, it includes assessment and planning activities associated with complementary trust and key-establishment approaches, including enhanced key management architectures, distributed symmetric key systems, Secure Key Infrastructure (SKI), and Quantum Key Distribution (QKD)-enabled environments. Relevant infrastructure includes for example QKD transmitter and receivers, Q-KMS, and QRNG entropy sources.
2. Cryptographic Infrastructure Modernisation
Once a satisfactory level of cryptographic visibility has been attained, risks understood, and transition plans agreed, the next stage (though it’s not a strictly linear process) is the modernisation of the cryptographic infrastructure itself. This includes upgrading, replacing or rearchitecting platforms such as Hardware Security Modules (HSMs), Public Key Infrastructure (PKI), certificate lifecycle management (CLM), key management systems (KMS), cryptographic libraries and related trust services.
Over time, these platforms will increasingly support crypto-agile and standards-based PQC capabilities through vendor hardware, software and service upgrades. During the transition period, organisations are likely to operate hybrid cryptographic environments where classical and quantum-safe certificates, keys, algorithms and protocols must coexist until interoperability, assurance, performance and regulatory requirements are fully resolved. As a result, organisations will need to manage parallel trust models, migration workflows and lifecycle processes across both legacy and QS-capable environments.
Implementation of quantum-safe practices is also likely to accelerate refresh cycles within cryptographic infrastructure due to increasing key management complexity, hybrid operational requirements, performance considerations and vendor-driven upgrade programmes. In some cases, organisations may require new hardware platforms to support higher cryptographic workloads, improved cryptographic abstraction, hardware acceleration or compliance with emerging PQC standards and assurance requirements.
3. Crypto-Dependent Infrastructure Modernisation
Crypto-dependent infrastructure refers to IT, networking, cloud, telecommunications, endpoint and operational technology platforms that rely on cryptography as an embedded capability rather than as the primary product function. Examples include networking hardware, firewalls, routers, telecom infrastructure, cloud platforms, operating systems, servers, endpoints, industrial control systems and connected devices.
In these environments, quantum-safe capabilities are typically incorporated into underlying cryptographic libraries, protocols, firmware or operating system components and are rarely monetised as standalone cryptographic products. As PQC standards mature, many infrastructure platforms will become quantum-safe by default through normal hardware and software refresh cycles, with QS functionality integrated directly into the broader infrastructure stack.
The complexity of transition within crypto-dependent infrastructure varies significantly depending on the architecture and lifecycle characteristics of the underlying systems. In many enterprise and cloud environments, crypto-agile architectures and modular cryptographic libraries allow new algorithms and protocols to be introduced through software or firmware updates, making migration comparatively straightforward. However, in constrained, embedded, industrial and telecom environments, transition complexity may be driven by hardware dependencies, deterministic operational requirements, latency sensitivity, memory constraints, certification requirements and long asset lifecycles.
In some cases, legacy systems may be unable to support replacement algorithms because cryptographic functions are hardwired into hardware or firmware, or because the underlying platforms lack sufficient processing capability, memory or architectural flexibility to support new cryptographic implementations. In these environments, migration toward quantum-safe capability may require accelerated infrastructure replacement, network redesign or broader platform modernisation programmes.
Conclusion
For enterprises, the real question is therefore not simply “how much will QS cost?”, rather it is “which category of spend are we discussing, who owns the risk, and who is responsible for funding the transition?” The organisations that understand these distinctions early will be better positioned to forecast spend, prioritise remediation and avoid discovering too late that their biggest QS migration cost is not cryptography itself, but the infrastructure that was never designed to change.